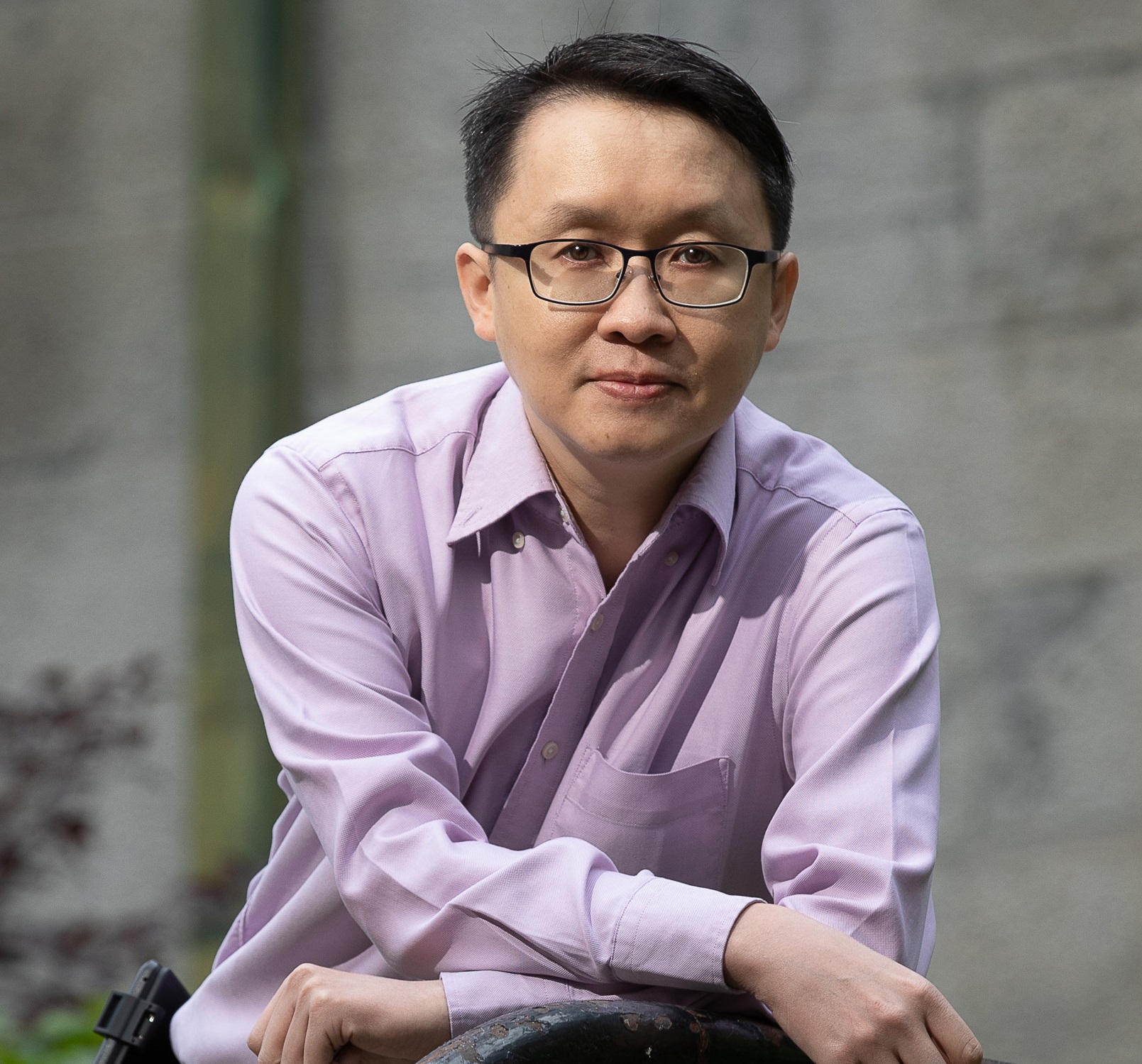
[By Year] [By Type] [By Google Scholar] [By DBLP] [By RG] [By ORCID]This page contains the preprint/postprint versions of my published articles. The articles are limited to personal use only. You may find the official versions and the copyright notices from the publishers' websites. Students and postdoctoral fellows under my supervision in the projects are underlined. |
|
Selected Publications [click here for a complete list by year] |
||
| [290] |
H. Yu, F. Khan, S. H. H. Ding, J. Wu, N. Stakhanova, and B. C. M. Fung.
Security risk assessment of Android automotive OS software supply chain using firmware reverse engineering. Computers & Security (COSE),
167(104923):1-19, August 2026. Elsevier. [ full paper | bibtex | JCR impact factor: 5.4, 5-year: 5.9 ] |
|
| [289] |
J. Wu, B. C. M. Fung, N. Stakhanova, F. Khan, and H. Yu.
Securing automotive data flow: a survey of telematics security across intra-vehicle, V2X, and
cloud layers. Vehicular Communications (VEHCOM),
59(101024):1-20, June 2026. Elsevier. [ full paper | bibtex | JCR impact factor: 6.5, 5-year: 7.3 ] |
|
| [287] |
A. R. Sarkar, F. J. Sarmin, D. Mouheb, B. C. M. Fung, and N. Mohammed.
Assessment of differentially private fine-tuning of large language models for
synthetic clinical note generation. Intelligent Systems with Applications (ISWA),
30(200659):1-11, May2026.
Elsevier. [ full paper | bibtex | JCR impact factor: 4.3, 5-year: 4.5 ] |
|
| [286] |
A. Bodaghi, B. C. M. Fung, and K. A. Schmitt.
PPO-CIS: A
deep reinforcement learning Framework for real-time toxicity
detection in social media. Knowledge-Based Systems (KBS),
341(115704):1-17, May 2026. Elsevier. [ full paper | bibtex | JCR impact factor: 7.6, 5-year: 7.6 ] |
|
| [280] |
M. Saqib, B. C. M. Fung, and P.
Charland. PAC-X: fuzzy explainable AI for multi-class malware detection. IEEE Transactions on Fuzzy Systems (TFS),
34(1):53-64, January 2026. IEEE Press. [ full paper | bibtex | software | JCR impact factor: 11.9, 5-year: 10.8 ] |
|
| [278] |
H. Ismail, M. A. Serhani, and B. C. M. Fung. Enhanced
multi-class arrhythmia detection using generative adversarial networks for minority
class augmentation. Cognitive Computation, 18(6):1-18,
January 2026.
Springer
Nature. [ full paper | bibtex | JCR impact factor: 4.3, 5-year: 4.1 ] |
|
| [277] |
M. Amouei, B. C. M. Fung, and
P. Charland. FIN: boosting binary code embedding by normalizing function
inlinings. Journal of Systems and Software
(JSS),
231(112603):1-20, January 2026.
Elsevier. [ full paper | bibtex | software | JCR impact factor: 4.1, 5-year: 4.1 ] |
|
| [276] |
M. Q. Li and B. C. M. Fung. Security
concerns for large language models: a survey. Journal of Information Security and Applications (JISA),
95(104284):1-18, December 2025. Elsevier. [ full paper | bibtex | JCR impact factor: 3.7, 5-year: 4.3 ] |
|
| [275] |
S. Bellemare,
D. Migault,
B. C. M. Fung,
S. Preda, and A. Boukhtouta. CSyncProxy: differentially private third-party
cookie synchronization. In Proceedings
of the 2025 IEEE Global Communications Conference (GLOBECOM): Communication
and Information Systems Security (CISS), 7
pages, Taipei, Taiwan: IEEE Press, December 2025. [ symposium full paper | bibtex | software | acceptance rate: 1078/2730 = 39.49% ] |
|
| [273] |
L. Li, L. Song, S. H. H. Ding,
B. C. M. Fung, and P. Charland.
Transforming generic coder LLMs to effective binary code embedding models for similarity detection.
In Proceedings of the 39th Annual Conference on Neural Information Processing Systems (NeurIPS),
17 pages, San Diego, CA, November 2025. [ full paper | poster | slides | bibtex ] |
|
| [269] |
A. Bodaghi, B. C. M. Fung, and K. A.
Schmitt. AugmenToxic: leveraging reinforcement learning to optimize LLM instruction
fine-tuning for data augmentation to enhance toxicity detection. ACM
Transactions on the Web (TWEB): Special Issue on Advances in Social Media Technologies and Analysis,
19(4.38):1-41. October 2025. ACM. [ full paper | bibtex | JCR impact factor: 2.6, 5-year: 2.8 ] |
|
| [268] |
S. Hogue, M. Lavallée, and B. C. M. Fung. Countering foreign
disinformation: building a resilient Canadian democracy through stronger
education and regulation. International
Journal: Canada's Journal of Global Policy Analysis, 80(3):513-523,
September 2025.
SAGE. [ full paper | bibtex | JCR impact factor: 2.3, 5-year: 2.3 ] |
|
| [267] |
M. Saqib,
B. C. M. Fung,
S. H. H. Ding, and P. Charland.
MalGPT: a generative explainable model for malware binaries. In Proceedings
of the European Conference on Machine Learning and Principles and Practice of Knowledge Discovery in Databases (ECML PKDD)
- Research Track (LNAI 16016), pages 130-148, Porto, Portugal, September 2025. [ research track full paper | bibtex | slides | software | acceptance rate: 24% ] |
|
| [262] |
A. Larosa, T. R. Zhang, A. S. Wong, C. Y. H. Fung,
X. L. Y. Long, P. Singh,
B. C. M. Fung, and T. P. Wong. Diminished social memory and hippocampal correlates of social interactions in chronic social defeat stress susceptibility. Biological Psychiatry: Global Open Science
(BGSGOS), 5(3.100455):1-10, May 2025. Elsevier. [ full paper | bibtex | JCR impact factor: 3.7, 5-year: 3.9 ] |
|
| [259] |
A. Abusitta,
M. Q. Li, and B. C. M. Fung.
Survey on explainable AI: techniques, challenges and
open issues. Expert Systems With Applications (ESWA),
255(C.124710):1-18, December 2024.
Elsevier. [ full paper | bibtex | JCR impact factor: 7.5, 5-year: 7.6 ] |
|
| [253] |
M. Saqib,
S. Mahdavifar, B. C. M. Fung, and P. Charland.
A comprehensive analysis of explainable AI for malware hunting. ACM
Computing Surveys (CSUR),
56(12.314):1-40, October 2024.
ACM. [ full paper | bibtex | JCR impact factor: 23.8, 5-year: 21.5 ] |
|
| [251] |
A. Bodaghi, K. A. Schmitt, P. Watine, and B.
C. M. Fung. A literature
review on detecting, verifying, and mitigating
online misinformation. IEEE
Transactions on Computational Social Systems (TCSS): Special Issue on Dark side of the Socio-Cyber World: Media Manipulation, Fake News, and Misinformation,
11(4):5119-5145, August 2024. IEEE. [ full paper | bibtex | JCR impact factor: 4.5, 5-year: 4.6 ] |
|
| [250] |
L. Li, S. H. H. Ding, A. Walenstein, P. Charland, and B. C. M. Fung. Dynamic
neural control flow execution: an agent-based deep
equilibrium approach for binary vulnerability detection. In
Proceedings of the 33rd ACM International Conference on Information and
Knowledge Management (CIKM), pages 1215-1225,
Boise, ID: ACM, October 2024. [ full paper | bibtex | acceptance rate: 347/1496=23% ] |
|
| [249] |
S. Mahdavifar,
M. Saqib,
B. C. M. Fung,
P. Charland, and A. Walenstein.
VulEXplaineR: XAI for vulnerability detection on
assembly code. In Proceedings
of the European Conference on Machine Learning and Principles and Practice of Knowledge Discovery in Databases (ECML PKDD),
pages 3-20, Vilnius, Lithuania: Springer, September 2024. [ applied data science track full paper | bibtex | slides | source code | acceptance rate: 55/224 = 24.5% ] |
|
| [248] |
D.-W. Jaw,
S.-C. Huang, Z.-H. Lu,
B. C. M. Fung,
and S.-Y.
Kuo.
Multi-domain object detection framework using
feature domain knowledge distillation.
IEEE Transactions on Cybernetics (CYB),
54(8):4643-4651, August 2024.
IEEE Systems, Man, and Cybernetics Society. [ full paper | bibtex | JCR impact factor: 9.4, 5-year: 10.3 ] |
|
| [245] |
J. F. Low, B. C. M. Fung,
and P. Xiong. Better entity matching with transformers through ensembles. Knowledge-Based Systems (KBS),
293(111678):1-11, June 2024. Elsevier. [ full paper | bibtex | JCR impact factor: 7.2, 5-year: 7.4 ] |
|
| [243] |
M. Saqib, B. C. M. Fung, P. Charland, and A. Walenstein. GAGE:
genetic algorithm-based graph explainer for malware analysis. In
Proceedings of the 40th IEEE International Conference on Data
Engineering (ICDE), pages 2258-2270,
Utrecht, Netherlands: IEEE Computer Society, May 2024. [ full paper | bibtex | slides | software | acceptance ratio: 337/1481 = 22.75% ] |
|
| [242] |
Y. Sun,
F. Haghighat, and B. C. M. Fung.
Fairness-aware data-driven based model predictive controller: a study on thermal
energy storage in a residential building. Journal of Energy Storage (EST),
87(111402):1-16, May 2024.
Elsevier. [ full paper | bibtex | JCR impact factor: 8.9, 5-year: 9.0 ] |
|
| [237] |
A. Bodaghi, B. C. M. Fung, and K. Schmitt.
Technological solutions to online toxicity: potential and pitfalls.
IEEE Technology and Society Magazine (TSM),
42(4):57-65, December 2023.
IEEE Society on Social Implications of Technology. [ full paper | bibtex | JCR impact factor: 2.1, 5-year: 2.7 ] |
|
| [233] |
C. W.
Cheong,
K. Yin, W. K. Cheung,
B. C. M. Fung,
and J. Poon.
Adaptive integration of categorical and multi-relational ontologies with EHR data for medical concept embedding.
ACM Transactions on Intelligent Systems and Technology (TIST),
14(6):111.1-111.20, November 2023.
ACM. [ full paper | bibtex | JCR impact factor: 7.2, 5-year: 8.5 ] |
|
| [230] |
L. Li, S. H. H. Ding,
Y. Tian, B. C. M. Fung,
P. Charland, W. Ou, L. Song, and C. Chen.
VulANalyzeR: explainable binary vulnerability detection with multi-task learning and attentional graph convolution.
ACM Transactions on Privacy and Security (TOPS),
26(3):28.1-28.25, August 2023. ACM. [ full paper | bibtex | JCR impact factor: 3.0, 5-year: 3.4 ] |
|
| [223] |
A. Abusitta,
G. H. S. de Carvalho, O. Abdel Wahab, T. Halabi, B. C. M. Fung, and
S. Al Mamoori.
Deep learning-enabled anomaly detection for IoT systems. Internet of Things (IoT),
21(100656):1-13, April 2023. Elsevier. [ full paper | bibtex | JCR impact factor: 6.0, 5-year: 6.2 ] |
|
| [221] |
R. H. Khokhar,
B. C. M. Fung,
F. Iqbal, K. Al-Hussaeni, and
M. Hussain.
Differentially private release of heterogeneous network for managing healthcare data.
ACM Transactions on Knowledge Discovery from Data (TKDD),
17(6):90.1-90.30. February 2023,
ACM. [ full paper | bibtex | JCR impact factor: 4.0, 5-year: 3.9 ] |
|
| [219] |
Y. Sun,
B. C. M. Fung, and F. Haghighat.
In-processing fairness improvement methods for regression data-driven building
models: achieving uniform energy prediction. Energy and Buildings (ENB),
277(11265):1-13, December 2022.
Elsevier. [ full paper | bibtex | JCR impact factor: 6.7, 5-year: 6.6 ] |
|
| [218] |
M. H. Altakrori, T. Scialom, B. C. M.
Fung, and
J. C. K. Cheung.
A multifaceted framework to evaluate evasion, content preservation, and misattribution in authorship obfuscation techniques. In
Proceedings
of the 2022 Conference on Empirical Methods in Natural Language
Processing (EMNLP), pages 2391-2403, Abu Dhabi, UAE: ACL,
December 2022. [ long paper with oral presentation | slides | video | bibtex ] |
|
| [213] |
K. Yin,
W. K. Cheung, B. C. M. Fung, and J. Poon.
Learning inter-modal correspondence and
phenotypes from multi-modal electronic health
records. IEEE Transactions on Knowledge and Data Engineering (TKDE),
34(9):4328-4341, September 2022. IEEE Computer Society. [ full paper | bibtex | JCR impact factor: 8.9, 5-year: 8.9 ] |
|
| [212] |
Y. Sun,
B. C. M. Fung, and F. Haghighat.
The generalizability of pre-processing techniques on the accuracy and fairness of data-driven building model: a case study. Energy and Buildings (ENB),
268(112204):1-19, August 2022. Elsevier. [ full paper | bibtex | JCR impact factor: 6.7, 5-year: 6.6 ] |
|
| [210] |
M. Q. Li, B. C. M. Fung, and
P. Charland.
DyAdvDefender: an instance-based online machine learning model for perturbation-trial-based
black-box adversarial defense. Information Sciences (INS),
601:357-373, July 2022. Elsevier. [ full paper | bibtex | JCR impact factor: 8.1, 5-year: 7.5 ] |
|
| [206] |
C. Molloy, S. H. H. Ding,
B. C. M. Fung,
and P. Charland.
H4rm0ny: a competitive zero-sum two-player markov game for multi-agent learning on
evasive malware generation and detection. In Proceedings of the IEEE International Conference on
Cyber Security and Resilience (CSR),
pages 22-29, Virtual Conference: IEEE Press, July 2022. [ full paper | bibtex | best research paper award - This award is established to recognize and promote high-quality regular research contributions to theoretical and practical aspects of security, privacy, trust, and resilience of networks, systems (including complex cyber-physical systems), applications, and services. ] |
|
| [194] |
Y. Sun,
F. Haghighat, and B. C. M. Fung.
Trade-off between accuracy and fairness of data-driven building and indoor
environment models: a comparative study of pre-processing methods. Energy
(EGY), 239(122273):1-16, January 2022.
Elsevier. [ full paper | bibtex | JCR impact factor: 8.9, 5-year: 8.2 ] |
|
| [193] |
J. F. Low, B. C. M. Fung,
F. Iqbal, and S.-C. Huang.
Distinguishing between fake news and satire with transformers. Expert Systems With Applications (ESWA),
187(115824):1-13, January 2022.
Elsevier. [ full paper | bibtex | software | JCR impact factor: 8.5, 5-year: 8.3 ] |
|
| [187] |
M. H. Altakrori,
J. C. K. Cheung, and
B. C. M. Fung.
The topic confusion task: a novel evaluation scenario for authorship attribution. In
Proceedings
of the 2021 Conference on Empirical Methods in Natural Language
Processing (EMNLP), pages 4242-4256, Punta Cana, Dominican Republic: ACL, November 2021. [ full paper | presentation | bibtex | software and datasets ] |
|
| [183] |
M. Q. Li,
B. C. M. Fung, P. Charland, and S. H. H. Ding.
I-MAD: interpretable malware detector using Galaxy
Transformer. Computers &
Security (COSE),
108(102371):1-15, September 2021. Elsevier. [ full paper | bibtex | software | JCR impact factor: 5.105, 5-year: 5.299 ] |
|
| [177] |
A. Abusitta,
M. Q. Li, and B. C. M. Fung.
Malware classification and composition analysis: a survey of recent
developments. Journal of Information Security and Applications (JISA),
59(102828):1-17, June 2021.
Elsevier. [ full paper | bibtex | JCR impact factor: 4.960, 5-year: 4.379 ] |
|
| [176] |
H. Bo, S. H.
H. Ding,
B. C. M. Fung, and F. Iqbal.
ER-AE: Differentially private
text generation for authorship anonymization. In Proceedings
of the 2021 Conference of the North American Chapter of the Association for Computational Linguistics: Human Language Technologies (NAACL-HLT),
pages 3997-4007, Virtual Conference, June 2021. Association for Computational Linguistics. [ full paper | poster | slides | video | bibtex | software ] |
|
| [172] |
K. Yin,
W. K. Cheung, B. C. M. Fung, and J. Poon.
TedPar: temporally dependent PARAFAC2 factorization for phenotype-based disease
progression modeling. In Proceedings
of the 21st SIAM
International Conference on Data Mining (SDM),
pages 594-602, Alexandria, VA: SIAM, May 2021. [ full paper | bibtex | acceptance ratio: 21.25% = 85/400 ] |
|
| [170] |
R. Wang,
B. C. M. Fung, Y. Zhu, and Q. Peng.
Differentially
private data publishing for arbitrarily partitioned data. Information
Sciences (INS),
553:247-265, April 2021. Elsevier. [ full paper | bibtex | JCR impact factor: 8.233, 5-year: 7.299 ] |
|
| [165] |
R. H. Khokhar,
F. Iqbal, B. C. M. Fung,
and J. Bentahar.
Enabling secure trustworthiness assessment and privacy protection in integrating
data for trading person-specific information. IEEE Transactions on Engineering Management (TEM) Special Section: Services Computing Management for Artificial Intelligence and Machine Learning,
68(1):149-169, February 2021. IEEE Publishing. [ full paper | bibtex | JCR impact factor: 8.702, 5-year: 7.388 ] |
|
| [164] |
S. A. Alkhodair,
B. C. M. Fung,
S. H. H. Ding, W. K. Cheung, and S.-C. Huang.
Detecting high-engaging breaking news rumors in social media. ACM Transactions on Management Information Systems (TMIS),
12(1):8.1-8.16,
December 2020. ACM Press. [ full paper | bibtex | JCR impact factor: 0.85 ] |
|
| [163] |
F. Iqbal,
M. Debbabi, and
B. C. M. Fung.
Machine Learning for Authorship Attribution and Cyber Forensics,
ser. Computer Entertainment and Media Technology. 194 pages, Springer Nature,
December 2020. [ book | bibtex | ISBN: 978-3-030-61674-8 ] |
 |
| [160] |
R. Wang,
B. C. M. Fung, and Y. Zhu.
Heterogeneous data release for cluster analysis with differential privacy. Knowledge-Based Systems (KBS),
201-202(106047):1-13, August 2020.
Elsevier. [ full paper | bibtex | JCR impact factor: 8.038, 5-year: 7.842 ] |
|
| [159] |
Y. Sun,
F. Haghighat, and B. C. M. Fung.
A review of the-state-of-the-art in
data-driven approaches for building energy
prediction. Energy and Buildings (ENB),
221(110022):1-23,
August 2020. Elsevier. [ full paper | bibtex | JCR impact factor: 5.879, 5-year: 6.175 ] |
|
| [157] |
G. G.
Dagher, B. C. M. Fung, N. Mohammed, and J. Clark.
SecDM:
privacy-preserving data outsourcing framework with differential privacy.
Knowledge and Information Systems (KAIS),
62(5):1923-1960, May 2020.
Springer. [ full paper | bibtex | JCR impact factor: 2.822, 5-year: 3.161 ] |
|
| [155] |
S. A. Alkhodair,
S. H. H. Ding,
B. C. M. Fung, and J. Liu.
Detecting breaking news rumors of emerging topics in social media.
Information Processing & Management (IP&M),
57(2.102018):1-13, March 2020. Elsevier. [ full paper | bibtex | JCR impact factor: 6.222, 5-year: 5.789 ] |
|
| [154] |
M. Ashouri, B. C. M. Fung, F. Haghighat, and H. Yoshino.
Systematic
approach to provide building occupants with feedback to reduce energy consumption.
Energy (EGY), 194(116813):1-9, March 2020.
Elsevier. [ full paper | bibtex | JCR impact factor: 7.147, 5-year: 6.845 ] |
|
| [138] |
L. Song,
C. W. Cheong, K. Yin, W. K. Cheung,
B. C. M. Fung, and J. Poon.
Medical concept embedding with multiple
ontological representations.
In
Proceedings of the 28th International Joint Conference on Artificial Intelligence (IJCAI),
pages 4613-4619, Macao, China, August 2019. [ full paper | bibtex | acceptance ratio: 850/4752 = 17.9% ] |
|
| [137] |
S. H. H. Ding,
B. C. M. Fung, and P. Charland.
Asm2Vec:
boosting static representation robustness for binary clone search
against code obfuscation and compiler optimization.
In
Proceedings of the 40th IEEE Symposium on Security and Privacy (S&P),
pages 38-55, San Francisco, CA:
IEEE Computer Society, May 2019. [ full paper | bibtex | video | software and source code: Kam1n0: Asm2Vec | acceptance ratio: 84/679 = 12.4% | collaborated with Defence Research & Development Canada (DRDC) ] |
|
| [134] |
S. H. H. Ding,
B. C. M. Fung, F. Iqbal, and W. K. Cheung.
Learning stylometric representations for authorship analysis.
IEEE Transactions on Cybernetics (CYB),
49(1):107-121,
January 2019.
IEEE Systems, Man, and Cybernetics Society. [ full paper | bibtex | software with source code - StyloMatrix | JCR impact factor: 11.079, 5-year: 10.090 ] |
|
| [133] |
K. Yin,
D. Qian, W. K. Cheung,
B. C. M. Fung, and J. Poon.
Learning phenotypes and dynamic patient representations via RNN regularized
collective non-negative tensor factorization.
In
Proceedings of the 33rd AAAI Conference on Artificial Intelligence (AAAI),
pages 1246-1253, Honolulu, HI, January 2019. [ full paper with oral presentation | bibtex | acceptance ratio: 1150/7095 = 16.2% ] |
|
| [132] |
M. Ashouri, F. Haghighat, B. C. M. Fung, and H. Yoshino.
Development of a ranking procedure for energy performance evaluation of buildings based on occupant behavior.
Energy and Buildings (ENB),
183:659-671, January 2019. Elsevier. [ full paper | bibtex | JCR impact factor: 4.867, 5-year: 5.055 ] |
|
| [130] |
M. H. Altakrori,
F. Iqbal,
B. C. M. Fung,
S. H. H. Ding, and A. Tubaishat.
Arabic authorship attribution: an extensive study on Twitter posts.
ACM Transactions on Asian and Low-Resource Language Information Processing (TALLIP),
18(1):5.1-5.51, November 2018.
ACM Press. [ full paper | bibtex | JCR impact factor: 0.788, 5-year: 0.768 ] |
|
| [129] |
K. Al-Hussaeni,
B. C. M. Fung, F. Iqbal,
G. G. Dagher,
and E. Park. SafePath: differentially-private publishing of passenger trajectories in transportation systems.
Computer Networks (COMNET): Special Issue on Intelligent and Connected Transportation Systems,
143:126-139, October 2018. Elsevier. [ full paper | bibtex | JCR impact factor: 3.030, 5-year: 2.989 ] |
|
| [128] |
K. Al-Hussaeni,
B. C. M. Fung, F. Iqbal, J. Liu,
and P. C. K. Hung. Differentially private multidimensional data publishing.
Knowledge and Information Systems (KAIS): An International Journal,
56(3):717-752, September 2018. Springer. [ full paper | bibtex | software with source code - DiffMulti | JCR impact factor: 2.397, 5-year: 2.547 ] |
|
| [126] |
M. Ashouri, F. Haghighat, B. C. M. Fung,
A. Lazrak, and H. Yoshino. Development of building energy saving advisory: a data mining approach.
Energy and Buildings (ENB), 172:139-151, August 2018.
Elsevier. [ full paper | bibtex | JCR impact factor: 4.495, 5-year: 4.823 ] |
|
| [125] |
K. Yin,
W. K. Cheung, Y. Liu, B. C. M. Fung, and J. Poon.
Joint learning of phenotypes and diagnosis-medication correspondence via hidden
interaction tensor factorization. In
Proceedings of the 27th International Joint Conference on Artificial
Intelligence (IJCAI),
pages 3627-3633, Stockholm, Sweden, July 2018. [ full paper | bibtex | acceptance ratio: 710/3470 = 20% ] |
|
| [122] |
J. Liu, X. Zhang, B. C. M.
Fung, J. Li, and F. Iqbal. Opportunistic mining of top-n high utility patterns.
Information Sciences (INS), 441:171-186, May 2018. Elsevier. [ full paper | bibtex | JCR impact factor: 5.524, 5-year: 5.305 ] |
|
| [121] |
T.
Braun, B. C. M. Fung,
F. Iqbal, and B. Shah.
Security and privacy challenges in smart cities.
Sustainable Cities and Society (SCS): Special Issue on Towards Secure, Privacy-Preserving, and Reliable Smart Cities and Society,
39:499-507, May 2018. Elsevier. [ full paper | bibtex | JCR impact factor: 4.624, 5-year: 4.466 | acceptance ratio: 499/2381 = 20.96% | the 9th most cited article in 2017 | the 9th most downloaded article in 2018 | one of the top 25 most downloaded articles in SCS ] |
|
| [120] |
S. A. Alkhodair,
B. C. M. Fung, O. Rahman, and P. C. K. Hung.
Improving interpretations of topic modeling in microblogs.
Journal of the Association for Information Science and Technology (JASIST),
69(4):528-540, April 2018. Wiley-Blackwell. [ full paper | bibtex | JCR impact factor: 2.738, 5-year: 3.101 ] |
|
| [112] |
J. Guo, B. C. M. Fung,
F. Iqbal, P. J. K. Kuppen, R. A. E. M. Tollenaar,
W. E. Mesker, and J.-J. Lebrun.
Revealing determinant factors for early
breast cancer recurrence by decision tree.
Information Systems Frontiers (ISF),
19(6):1233-1241, December 2017.
Springer. [ full paper | bibtex | JCR impact factor: 3.232, 5-year: 2.563 ] |
|
| [110] |
L.
Guerrouj, Z. Kermansaravi, V. Arnaoudouva, B. C. M. Fung, F. Khomh, G. Antoniol, and
Y.-G. Guéhéneuc.
Investigating the relation between lexical smells
and change- and fault-proneness: an empirical study. Software Quality Journal (SQJO),
25(3):641-670, September 2017. Springer. [ full paper | bibtex | JCR impact factor: 1.596, 5-year: 1.903 ] |
|
| [101] |
Z. Yu,
F. Haghighat, and B. C. M. Fung.
Advances and challenges in building engineering and data mining applications for energy-efficient communities. Sustainable Cities and Society (SCS),
25:33-38, August 2016. Elsevier. [ full paper | bibtex | open access | JCR impact factor: 1.777, 5-year: 1.968 | the 6th and 10th most downloaded article of SCS in 2017 and 2018, respectively ] |
|
| [100] |
S. H. H.
Ding, B. C. M. Fung, and P. Charland.
Kam1n0: MapReduce-based assembly clone search for reverse engineering. In
Proceedings of the 22nd ACM SIGKDD International Conference on
Knowledge Discovery and Data Mining (SIGKDD), pages
461-470, San
Francisco, CA: ACM Press, August 2016. [ full paper with poster presentation | bibtex | video | slides | poster | software and source code: Kam1n0: Asm-Clone | Hex-Rays plug-in contest award | acceptance ratio: (70+72)/784 = 18% | collaborated with Defence Research & Development Canada (DRDC) ] |
|
| [97] |
J. Liu, K. Wang, and B. C. M. Fung.
Mining
high utility patterns in one phase without generating candidates. IEEE Transactions on Knowledge and Data Engineering (TKDE),
28(5):1245-1257, May 2016.
IEEE Computer Society. [ full paper | bibtex | JCR impact factor: 3.438, 5-year: 3.899 ] |
|
| [96] |
R. H. Khokhar, B. C. M. Fung,
F. Iqbal, D. Alhadidi, and J. Bentahar.
Privacy-preserving data mashup model for trading person-specific
information. Electronic Commerce Research and Applications (ECRA),
17:19-37, May-June 2016. Elsevier. [ full paper | bibtex | JCR impact factor: 1.954, 5-year: 3.181 ] |
|
| [91] |
M. R. Farhadi, B. C. M. Fung,
Y. B. Fung, P. Charland, S. Preda, and M. Debbabi.
Scalable
code clone search for malware analysis. Digital Investigation
(DIIN): Special Issue on Big Data and Intelligent Data Analysis,
15:46-60, December 2015.
Elsevier. [ full paper | bibtex | JCR impact factor: 1.211, 5-year: 1.436 ] |
|
| [85] |
M. Schmid,
F. Iqbal, and B. C. M. Fung.
E-mail
authorship attribution using customized associative classification. Digital Investigation
(DIIN), 14(1):S116-S126,
August 2015. Elsevier. [ full paper | bibtex | this journal article was presented in the 15th ACM DFRWS | acceptance ratio = 16/46 = 34.8% | JCR impact factor: 1.211, 5-year: 1.436 ] |
|
| [84] |
S. H. H. Ding, B. C. M. Fung, and
M. Debbabi. A visualizable evidence-driven approach for authorship attribution. ACM Transactions on Information and System Security (TISSEC),
17(3):12.1-12.30, March 2015. ACM Press. [ full paper | bibtex | JCR impact factor: 0.759, 5-year: 1.610 | SJR impact factor: 1.772 ] |
|
| [81] |
B. C. M. Fung,
Y. Jin, J. Li, and J. Liu.
Recommendation and Search in Social Networks,
chapter Anonymizing social network data for
maximal frequent-sharing pattern mining.
Lecture
Notes in Social Networks (LNSN), pages 77-100,
February 2015. Springer. [ book chapter | bibtex | This book chapter is an extension of ASONAM13. ] |
|
| [80] |
S. Li, K. Nahar, and B. C. M. Fung.
Product
customization of tablet computers based on the information of online reviews by
customers. Journal of Intelligent Manufacturing
(JIM), 26(1):97-110, February 2015.
Springer. [ full paper | bibtex | JCR impact factor: 1.995, 5-year: 2.159 ] |
|
| [79] |
K. Al-Hussaeni, B. C. M. Fung, and
W. K. Cheung. Privacy-preserving trajectory stream publishing. Data & Knowledge Engineering (DKE),
94(A):89-109, November 2014. Elsevier. [ full paper | bibtex | software with source code - ITSA | JCR impact factor in 2014: 1.115, 5-year: 1.594 ] |
|
| [78] |
S. Goryczka, L. Xiong, and B. C. M. Fung.
m-privacy for collaborative data publishing. IEEE Transactions on Knowledge and Data Engineering (TKDE),
26(10):2520-2533, October 2014.
IEEE Computer Society. [ full paper | bibtex | JCR impact factor in 2014: 2.067, 5-year: 2.873 ] |
|
| [77] |
R. Chen, B. C. M. Fung,
P. S. Yu, and B. C. Desai. Correlated network data publication via differential
privacy.
Very Large Data Bases Journal (VLDBJ),
23(4):653-676, August 2014.
Springer. [ full paper | bibtex | poster | JCR impact factor in 2014: 1.568, 5-year: 2.300 ] |
|
| [76] |
R. H. Khokhar,
R. Chen, B. C. M. Fung,
and S. M. Lui.
Quantifying the costs and benefits of privacy-preserving health data publishing.
Journal of Biomedical Informatics (JBI): Special Issue on Informatics Methods in Medical Privacy,
50:107-121, August 2014.
Elsevier. [ full paper | bibtex | JCR impact factor in 2014: 2.126, 5-year: 3.398 ] |
|
| [73] |
A. Basher and B. C. M. Fung.
Analyzing
topics and authors in chat logs for crime investigation.
Knowledge and Information Systems (KAIS): An International Journal,
39(2):351-381, May 2014.
Springer. [ full paper | bibtex | JCR impact factor in 2014: 1.782, 5-year: 2.016 ] |
|
| [70] |
N. Mohammed, D. Alhadidi, B. C. M. Fung,
and M. Debbabi. Secure two-party differentially private data release for
vertically-partitioned data. IEEE Transactions on Dependable and Secure Computing
(TDSC),
11(1):59-71, January/February 2014. IEEE Computer Society. [ full paper | bibtex | JCR impact factor in 2014: 1.351, 5-year: 1.652 ] |
|
| [69] |
M. Ghasemzadeh, B. C. M. Fung,
R. Chen, and A. Awasthi.
Anonymizing trajectory data for passenger flow analysis.
Transportation Research Part C: Emerging Technologies (TRC):
An International Journal, 39:63-79, February 2014.
Elsevier. [ full paper | bibtex | source code - TALF | JCR impact factor in 2014: 2.818, 5-year: 3.402 ] |
|
| [67] |
B. C. M. Fung,
Y. Jin, and J. Li.
Preserving privacy and frequent
sharing patterns for
social network data publishing. In Proceedings of the 5th IEEE/ACM
International Conference on Social Networks Analysis and Mining (ASONAM),
pages 479-485, Niagara Falls, Canada:
IEEE Computer Society, August 2013. [ short paper | bibtex | acceptance ratio: 28% = 13% + 15% ] |
|
| [65] |
G. G. Dagher and
B. C. M. Fung. Subject-based semantic document clustering for digital forensic investigations. Data & Knowledge Engineering (DKE),
86:224-241, July 2013. Elsevier. [ full paper | bibtex | CTV Interview | JCR impact factor in 2013: 1.489, 5-year: 1.609 ] |
|
| [64] |
Z. Yu, B. C. M. Fung,
and
F. Haghighat. Extracting knowledge from building-related data - a data mining framework. Building Simulation
(BUIL): An International Journal,
6(2):207-222, June 2013.
Springer. [ full paper | bibtex | JCR impact factor in 2013: 0.631, 5-year: 0.687 ] |
|
| [63] |
N. Mohammed, X. Jiang, R.
Chen, B. C. M. Fung, and L.
Ohno-Machado.
Privacy-preserving heterogeneous health data sharing.
Journal of the American Medical Informatics Association (JAMIA),
20(3):462-469, May 2013.
BMJ. [ full paper | bibtex | software with source code - DiffGen-Hetero | JCR impact factor in 2013: 3.932, 5-year: 4.182 ] |
|
| [62] |
R. Chen, B. C. M. Fung,
N. Mohammed, B. C. Desai, and K. Wang.
Privacy-preserving trajectory data publishing by local suppression.
Information Sciences (INS): Special Issue on Data Mining for Information
Security, 231:83-97, May 2013.
Elsevier. [ full paper | bibtex | JCR impact factor in 2013: 3.893, 5-year: 3.969 ] [ This paper presents a local suppression method to achieve LKC-privacy for trajectory data published by a single data provider. ] |
|
| [61] |
F. Iqbal, H. Binsalleeh, B. C. M. Fung,
and
M. Debbabi.
A unified data mining solution for authorship
analysis in anonymous textual communications. Information Sciences (INS): Special Issue
on Data Mining for Information
Security, 231:98-112, May 2013.
Elsevier. [ full paper | bibtex | JCR impact factor in 2013: 3.893, 5-year: 3.969 ] |
|
| [59] |
Y. Zeng, K.-Y. Kim, V. Raskin, B. C. M. Fung,
and
Y. Kitamura (Eds.). Advanced Engineering Informatics (ADVEI): Special Issue on
Modeling, Extraction, Transformation of Semantics in Computer Aided
Engineering Systems,
27(1), January 2013.
Elsevier. [ editorial | bibtex | JCR impact factor in 2012: 1.593, 5-year: 1.708 ] |
|
| [58] |
J. Liu, K.
Wang, and B. C. M. Fung. Direct discovery of high utility itemsets without candidate generation. In
Proceedings of the 12th IEEE International Conference on Data Mining (ICDM),
pages 984-989, Brussels, Belgium:
IEEE Computer Society, December 2012. [ short paper | bibtex | acceptance ratio: 20% = (81+70)/756 ] |
|
| [56] |
L. Bonomi, L. Xiong,
R. Chen, and B. C. M. Fung.
Frequent grams based embedding for privacy preserving record linkage. In
Proceedings of the 21st ACM Conference on Information and Knowledge
Management (CIKM), pages 1597-1601, Maui, HI: ACM Press, October 2012. [ database track short paper | bibtex | acceptance ratio: 27.7% = (146+156)/1088 ] |
|
| [55] |
P. Charland,
B. C. M. Fung,
and M. R. Farhadi. Clone search for malicious
code correlation. In Proceedings of the NATO RTO Symposium on Information
Assurance and Cyber Defense (STO-MP-IST-111),
pages 1.1-1.12, Koblenz, Germany, September 2012. [ full paper | bibtex | first runner-up for the best paper award ] |
|
| [54] |
R. Chen,
B. C. M. Fung,
B. C. Desai, and N. M. Sossou. Differentially private transit data
publication: a case study on the Montreal transportation system. In Proceedings of the
18th ACM SIGKDD International Conference on Knowledge Discovery and Data
Mining (SIGKDD), pages 213-221,
Beijing, China: ACM Press, August 2012. [ full paper with oral presentation | slides | poster | bibtex | acceptance ratio: 17.6% = 133/755 ] [ This paper presents a differentially-private sanitization method for sequential data published by a single data provider. ] |
|
| [53] |
B. C. M. Fung, T. Trojer, P. C.
K. Hung, L. Xiong, K. Al-Hussaeni, and
R. Dssouli. Service-oriented architecture for high-dimensional private data mashup.
IEEE Transactions on Services Computing (TSC),
5(3):373-386, July-September 2012.
IEEE Computer Society. [ full paper | bibtex | JCR impact factor in 2012: 2.460 | the Spotlight Paper for the July-September 2012 issue ] [ This paper presents a SOA to achieve LKC-privacy in a vertically-partitioned data owned by different data providers. ] |
|
| [52] |
D. Alhadidi, N. Mohammed,
B. C. M. Fung, and M. Debbabi. Secure distributed framework
for achieving ε-differential privacy. In Proceedings of the 12th
Privacy Enhancing Technologies Symposium (PETS),
LNCS 7834, pages 120-139, Vigo, Spain:
Springer-Verlag, July
2012. [ full paper | slides | bibtex | acceptance ratio: 22.2% = 16/72 ] [ This paper presents a secure protocol to achieve differential privacy in a horizontally-partitioned data owned by different data providers. ] |
|
| [51] |
Z. Yu, F. Haghighat, B. C. M. Fung, and
L. Zhou. A novel methodology for knowledge discovery through mining
associations between building operational data.
Energy and Buildings (ENB), 47:430-440, April 2012.
Elsevier. [ full paper | bibtex | JCR impact factor in 2012: 2.679, 5-year: 3.254 ] |
|
| [49] |
R. Al-Zaidy, B. C. M. Fung, A.
M. Youssef, and
F. Fortin. Mining criminal networks from unstructured text documents.
Digital Investigation (DIIN), 8(3-4):147-160, February 2012.
Elsevier. [ full paper | bibtex | JCR impact factor in 2014: 1.648, 5-year: 1.318 ] |
|
| [47] |
Z. Yu, F. Haghighat, B. C. M. Fung,
E. Morofsky, and H. Yoshino. A methodology for identifying and improving occupant behavior in residential buildings.
Energy,
36(11):6596-6608, November 2011.
Elsevier. [ full paper | bibtex | JCR impact factor in 2013: 4.159, 5-year: 4.465 ] |
|
| [44] |
N. Mohammed, B. C. M. Fung, and
M. Debbabi. Anonymity meets game theory: secure data integration with malicious
participants.
Very Large Data Bases Journal (VLDBJ),
20(4):567-588, August 2011.
Springer. [ full paper | bibtex | JCR impact factor in 2013: 1.701, 5-year: 2.111 ] [ This paper presents a secure protocol to achieve k-anonymity in a vertically-partitioned data owned by different malicious data providers. ] |
|
| [43] |
R. Chen,
N. Mohammed,
B. C. M. Fung, B. C. Desai, and L. Xiong.
Publishing
set-valued data via differential privacy. The Proceedings of the VLDB
Endowment (PVLDB), 4(11):1087-1098,
August 2011. VLDB Endowment. [ research track full paper | slides | bibtex | source code - DiffPart | this journal paper was presented at the 37th International Conference of Very Large Data Bases (VLDB 2011) | acceptance ratio: 18.1% = 100/553 ] [ This paper presents a differentially-private sanitization method for transaction data published by a single data provider. ] |
|
| [42] |
N. Mohammed,
R. Chen,
B. C. M. Fung,
and P. S. Yu.
Differentially private data release for data mining. In Proceedings of the
17th ACM SIGKDD International Conference on Knowledge Discovery and Data
Mining (SIGKDD),
pages 493-501,
San Diego, CA: ACM Press, August 2011. [ full paper with oral presentation | slides | poster | bibtex | software with source code - DiffGen | acceptance ratio (with oral presentation): 7.8% = 56/714 ] [ This paper presents a differentially-private sanitization method for relational data published by a single data provider. ] |
|
| [41] |
Z. Yu, B. C. M. Fung, F. Haghighat, H. Yoshino, and E. Morofsky.
A
systematic procedure to study the influence of occupant behavior on building
energy consumption.
Energy and Buildings (ENB), 43(6):1409-1417, June 2011.
Elsevier. [ full paper | bibtex | JCR impact factor in 2012: 2.679, 5-year: 3.254 | one of the most cited articles in ENB since 2010 ] |
|
| [37] |
N. Mohammed, B. C. M. Fung, P.
C. K. Hung, and C. Lee.
Centralized and distributed anonymization for high-dimensional healthcare
data. ACM Transactions on Knowledge Discovery from Data (TKDD),
4(4):18:1-18:33, October 2010. ACM Press. [ full paper | bibtex | JCR impact factor in 2012: 1.676 ] [ This paper presents a secure protocol to achieve LKC-privacy in a horizontally-partitioned data owned by different data providers. ] |
|
| [36] |
F.
Iqbal, H. Binsalleeh, B. C. M. Fung, and M. Debbabi.
Mining writeprints from anonymous e-mails for forensic investigation. Digital Investigation
(DIIN),
7(1-2):56-64, October 2010. Elsevier. [ full paper | bibtex | JCR impact factor in 2010: 0.836, 5-year: 1.043 ] |
|
| [34] |
P. Shi, L. Xiong, and B. C. M. Fung.
Anonymizing data with
quasi-sensitive attribute values. In
Proceedings of the 19th ACM Conference on Information and Knowledge
Management (CIKM), pages 1389-1392, Toronto, Canada: ACM Press, October 2010. [ database track short paper | poster | bibtex | acceptance ratio: 34.7% = (123+171)/847 ] |
|
| [33] |
Z. Yu, F. Haghighat, B. C. M. Fung, and
H. Yoshino. A decision tree method for building energy demand modeling.
Energy and Buildings (ENB), 42(10):1637-1646, October 2010.
Elsevier. [ full paper | bibtex | JCR impact factor in 2010: 2.046, 5-year: 2.256 ] |
|
| [31] |
B. C. M. Fung, K. Wang, A. W.-C. Fu, and P. S. Yu.
Introduction to Privacy-Preserving Data Publishing: Concepts and Techniques,
ser. Data Mining and Knowledge Discovery. 376 pages, Chapman & Hall/CRC,
August
2010. [ book | bibtex | ISBN: 9781420091489 ] |
 |
| [30] |
B. C. M. Fung, K. Wang, R.
Chen, and P. S. Yu. Privacy-preserving data publishing: a survey of recent
developments. ACM Computing Surveys (CSUR),
42(4):14.1-14.53, June 2010. ACM
Press. [ full paper | bibtex | JCR impact factor in 2010: 8.000, 5-year: 10.910 | cited by the U.S. Department of Commerce’s National Institute of Standards and Technology (NIST) in NIST IR 8053 DRAFT "De-Identification of Personally Identifiable Information" | This is the most cited article in Concordia University according to ACM Digital Library. ] |
|
| [27] |
N. Mohammed, B. C. M. Fung, and
M. Debbabi. Walking in the crowd: anonymizing trajectory data for
pattern analysis. In
Proceedings of the 18th ACM Conference on Information and Knowledge
Management (CIKM), pages 1441-1444, Hong Kong: ACM Press, November 2009. [ database track short paper | poster | bibtex ] [ This paper uses global suppressions to achieve LKC-privacy while preserving frequent sequences in trajectory data. See the technical report for details. ] |
|
| [26] |
T. Trojer, B. C. M. Fung,
and P. C. K. Hung. Service-oriented architecture for privacy-preserving data mashup. In
Proceedings of the 7th IEEE International Conference on Web Services
(ICWS), pages 767-774, Los Angeles, CA: IEEE Computer Society Press, July 2009. [ industrial track full paper | slides | bibtex | acceptance ratio: 18% = 61/339 ] [ See TSC11 for an extended version. ] |
|
| [25] |
N. Mohammed, B. C. M. Fung, P.
C. K. Hung, and C. Lee.
Anonymizing healthcare data: a case study on the
blood transfusion service. In Proceedings of the 15th ACM SIGKDD International
Conference on Knowledge Discovery and Data Mining (SIGKDD), pages
1285-1294, Paris,
France: ACM Press, June 2009. [ industrial track full paper | video presentation | slides | bibtex | software with source code - PAIS | acceptance ratio: 10% | best student paper award ] [ This paper presents an anonymization method to achieve LKC-privacy for relational data published by a single data provider. See TKDD10 for an extended version. ] |
|
| [24] |
B. C. M. Fung, K. Wang, L.
Wang, and P. C. K. Hung. Privacy-preserving data publishing for cluster
analysis. Data & Knowledge Engineering (DKE),
68(6):552-575, June 2009. Elsevier. [ full paper | bibtex | publisher link | JCR impact factor in 2009: 1.745, 5-year: 2.036 ] |
|
| [20] | N. Mohammed,
B. C. M. Fung, K. Wang, and P. C. K. Hung.
Privacy-preserving data mashup. In Proceedings of the 12th International Conference on Extending Database Technology (EDBT),
pages 228-239, Saint-Petersburg, Russia: ACM Press, March 2009. [ research track full paper | slides | bibtex | average acceptance ratio: 16% ] [ See VLDBJ11 for an extended version to malicious participants. ] [ See ICWS11 and TSC11 for extensions to SOA and high-dimensional data anonymization. ] |
|
| [18] | Y. Xu,
B. C. M. Fung, K. Wang, A. W. C. Fu, and J. Pei.
Publishing sensitive
transactions for itemset utility. In Proceedings of the 8th IEEE International Conference on Data Mining (ICDM),
pages 1109-1114, Pisa, Italy:
IEEE Computer Society, December 2008. [ short paper | slides | slides with audio | bibtex | acceptance ratio: 19.9% = (70+74)/724 ] |
[17] |
F.
Iqbal, R. Hadjidj,
B. C. M. Fung, and M. Debbabi.
A novel approach of mining write-prints for authorship attribution in e-mail
forensics. Digital Investigation (DIIN), 5(1):S42-S51.
September 2008. Elsevier. [ full paper | slides | bibtex | JCR impact factor in 2008: 0.961 | accepted 17 papers | this journal paper was presented in the 8th DFRWS | The research results were reported by media worldwide. ] |
| [15] |
B. C. M. Fung, K. Wang, L. Wang, and M. Debbabi.
A framework for privacy-preserving
cluster
analysis. In Proceedings of the 2008 IEEE International Conference on Intelligence and
Security Informatics (ISI), pages 46-51, Taipei, Taiwan, June 2008. [ full paper | slides | bibtex | acceptance ratio: 22% ] [ See DKE09 for an extended version. ] |
|
| [14] |
B. C. M. Fung, K. Wang, and M. Ester.
The Encyclopedia of Data Warehousing and Mining, 2nd ed., chapter
Hierarchical document clustering,
pages 970-975.
Idea Group, Hershey, PA, August 2008. [ book chapter | bibtex | © Idea Group ] |
|
| [13] |
B. C. M. Fung, K. Wang, A. W. C. Fu, and J. Pei.
Anonymity for continuous data publishing.
In Proceedings of the 11th International Conference on Extending Database Technology (EDBT), pages 264-275, Nantes, France: ACM Press, March 2008. [ research track full paper | slides | bibtex | research track acceptance ratio: 16.7% = 52/311 ] |
|
| [11] |
B. C. M. Fung, K. Wang, and P. S. Yu.
Anonymizing
classification data for privacy preservation. IEEE Transactions on Knowledge and Data Engineering (TKDE),
19(5):711-725, May 2007. IEEE Computer Society. [ full paper | bibtex | software with source code: TDS | JCR impact factor in 2009: 2.285, 5-year: 3.691 ] |
|
| [10] |
B. C. M. Fung. Privacy-preserving data publishing.
Ph.D. thesis, Simon Fraser University,
Burnaby, BC, Canada, May
2007.
[ thesis | bibtex ] |
|
| [9] | K. Wang,
B. C. M. Fung, and P. S. Yu.
Handicapping attacker's confidence:
an alternative to k-anonymization.
Knowledge and Information Systems (KAIS): An International Journal,
11(3):345-368, April 2007. Springer-Verlag. [ full paper | bibtex | JCR impact factor in 2009: 2.211, 5-year: 2.302 ] |
|
| [7] | K. Wang and
B. C. M. Fung. Anonymizing sequential releases.
In Proceedings of the
12th ACM SIGKDD International Conference on Knowledge Discovery and Data
Mining (SIGKDD), pages 414-423, Philadelphia, PA: ACM Press, August 2006. [ research track full paper | slides | bibtex | research track acceptance ratio: 10.9% = 50/457 ] |
|
| [6] | K. Wang,
B. C. M. Fung, and P. S. Yu.
Template-based
privacy preservation in classification
problems. In Proceedings of the 5th IEEE International Conference on Data Mining (ICDM), pages 466-473, Houston, TX:
IEEE Computer Society, November 2005. [ full paper | slides | bibtex | acceptance ratio: 11.0% = 69/630 ] [ Selected as one of the best papers to appear in Knowledge and Information Systems: An International Journal ] [ See KAIS07 for an extended version. ] |
|
| [5] |
B. C. M. Fung, K. Wang, and M. Ester.
The Encyclopedia of Data Warehousing and Mining, chapter
Hierarchical document clustering,
pages 555-559.
Idea Group, Hershey, PA, July 2005. [ book chapter | bibtex | © Idea Group ] |
|
| [4] | K. Wang,
B. C. M. Fung, and G. Dong.
Integrating
private databases for data analysis. In Proceedings of the 2005 IEEE International Conference on Intelligence and
Security Informatics (ISI), Lecture Notes in Computer Science (LNCS),
3495, pages 171-182, Atlanta, GA: Springer-Verlag, May 2005. [ full paper | slides | bibtex | © Springer-Verlag | accepted 28 full papers ] [ Selected as one of the best papers to appear in Knowledge and Information Systems ] [ See EDBT09 for an extended version. ] |
|
| [3] |
B. C. M. Fung, K. Wang, and P. S. Yu.
Top-down
specialization for information and privacy preservation. In Proceedings of the 21st IEEE International Conference on Data Engineering (ICDE), pages 205-216, Tokyo, Japan:
IEEE Computer Society, April 2005. [ research track full paper | slides | bibtex | software with source code: TDS | enhanced software with source code: SIGKDD09: PAIS | one of the top 3 most cited papers in ICDE05 | research track acceptance ratio: 12.9% = 67/521 ] [ See TKDE07 for an extended version. ] |
|
| [2] |
B. C. M. Fung, K. Wang, and M. Ester.
Hierarchical document clustering
using frequent itemsets. In Proceedings
of the 3rd SIAM
International Conference on Data Mining (SDM),
pages 59-70, San Francisco, CA: SIAM, May 2003. [ full paper | slides | bibtex | software - FIHC | acceptance ratio: 19.8% = 21/106 | Crawl-By-Example ] |
|